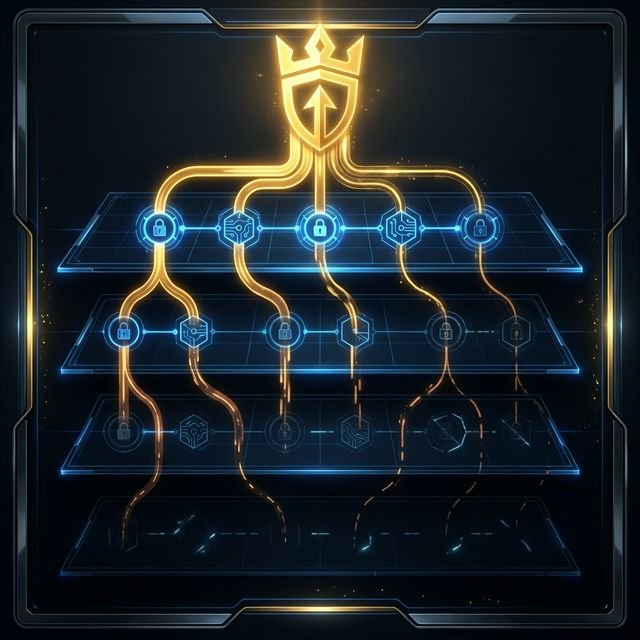
Three pillars. Three blind spots.
The common response
- Awareness training — teaches individuals what to avoid
- Policies — document rules and expected behaviour
- User vigilance — depends on constant, perfect attention
What they cannot address
- Situations where the action looks correct and is authorised
- Decisions made under legitimate pressure and urgency
- Trust that has not been revalidated under changed context
- Authority that was granted without containment or expiry

"Training teaches people what to avoid. It does not change the conditions that make avoidance irrelevant."
Beyond financial fraud.
The human attack surface is not limited to wire transfers or phishing. It operates in every workflow where trust, authority, and routine intersect.
HR Approvals
Access provisioned to a new hire before background verification is complete — because the request came from a senior leader and appeared routine.
IT Access
Administrative privileges granted to a contractor through an escalation chain that assumed each prior approval was verified. None were.
Vendor Onboarding
A trusted vendor's banking details changed mid-contract. The update was processed through normal channels, approved by authorised personnel, without revalidation.
Legal Sign-offs
A contract executed under time pressure, with authority delegated to someone without full context of the commercial terms or historical commitments.
This is where we work.
We analyse the structure of decisions, not the behaviour of individuals.