The Human Attack Surface
Framework
A structured method for identifying where authorised decisions, under plausible conditions, quietly become the primary source of irreversible damage.
How Legitimate Decisions Become Risk
How we see the problem.

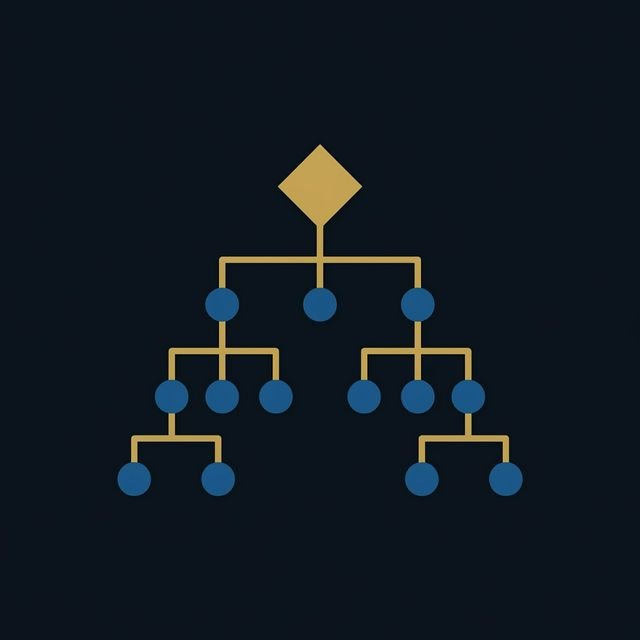
Authority Mapping
We map who holds authority over irreversible actions — and whether that authority is earned, inherited, or assumed. Authority without containment is the most common structural vulnerability.
Trust Path Analysis
We trace the trust chains behind critical decisions. Who was trusted, by whom, and on what basis? Trust that was valid yesterday may be invalid today under changed conditions.
Decision Containment
We identify decisions that, once executed, cannot be undone. Then we evaluate whether the process around each decision includes pause, verification, and reversibility — or assumes correctness.
Influence Resilience
We assess how susceptible critical workflows are to manipulation through urgency, social proof, or cascading authority. Resilience is not about awareness — it is about structural immunity.
This framework underpins all SecureArk engagements.